Journal Description
Mathematics
Mathematics
is a peer-reviewed, open access journal which provides an advanced forum for studies related to mathematics, and is published semimonthly online by MDPI. The European Society for Fuzzy Logic and Technology (EUSFLAT) and International Society for the Study of Information (IS4SI) are affiliated with Mathematics and their members receive a discount on article processing charges.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, SCIE (Web of Science), RePEc, and other databases.
- Journal Rank: JCR - Q1 (Mathematics) / CiteScore - Q1 (General Mathematics)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 16.9 days after submission; acceptance to publication is undertaken in 2.6 days (median values for papers published in this journal in the second half of 2023).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
- Sections: published in 13 topical sections.
- Companion journals for Mathematics include: Foundations, AppliedMath, Analytics, International Journal of Topology, Geometry and Logics.
Impact Factor:
2.4 (2022);
5-Year Impact Factor:
2.3 (2022)
Latest Articles
On Intersections of B-Spline Curves
Mathematics 2024, 12(9), 1344; https://doi.org/10.3390/math12091344 (registering DOI) - 28 Apr 2024
Abstract
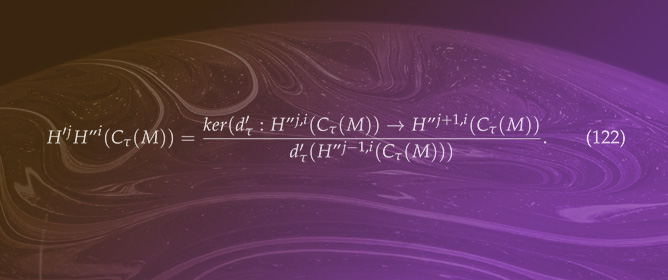
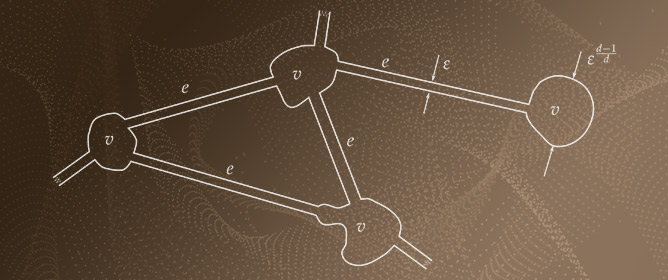
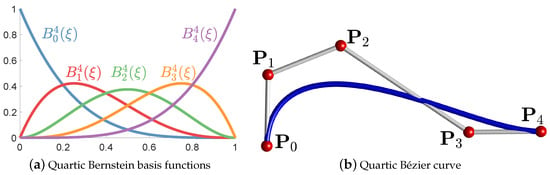
Bézier and B-spline curves are foundational tools for curve representation in computer graphics and computer-aided geometric design, with their intersection computation presenting a fundamental challenge in geometric modeling. This study introduces an innovative algorithm that quickly and effectively resolves intersections between Bézier and
[...] Read more.
Bézier and B-spline curves are foundational tools for curve representation in computer graphics and computer-aided geometric design, with their intersection computation presenting a fundamental challenge in geometric modeling. This study introduces an innovative algorithm that quickly and effectively resolves intersections between Bézier and B-spline curves. The number of intersections between the two input curves within a specified region is initially determined by applying the resultant of a polynomial system and Sturm’s theorem. Subsequently, the potential region of the intersection is established through the utilization of the pseudo-curvature-based subdivision scheme and the bounding box detection technique. The projected Gauss-Newton method is ultimately employed to efficiently converge to the intersection. The robustness and efficiency of the proposed algorithm are demonstrated through numerical experiments, demonstrating a speedup of 3 to 150 times over traditional methods.
Full article
(This article belongs to the Section Computational and Applied Mathematics)
►
Show Figures
Open AccessArticle
Improving Oriented Object Detection by Scene Classification and Task-Aligned Focal Loss
by
Xiaoliang Qian, Shaoguan Gao, Wei Deng and Wei Wang
Mathematics 2024, 12(9), 1343; https://doi.org/10.3390/math12091343 (registering DOI) - 28 Apr 2024
Abstract
Oriented object detection (OOD) can precisely detect objects with arbitrary direction in remote sensing images (RSIs). Up to now, the two-stage OOD methods have attracted more attention because of their high detection accuracy. However, the two-stage methods only rely on the features of
[...] Read more.
Oriented object detection (OOD) can precisely detect objects with arbitrary direction in remote sensing images (RSIs). Up to now, the two-stage OOD methods have attracted more attention because of their high detection accuracy. However, the two-stage methods only rely on the features of each proposal for object recognition, which leads to the misclassification problem because of the intra-class diversity, inter-class similarity and clutter backgrounds in RSIs. To address the above problem, an OOD model combining scene classification is proposed. Considering the fact that each foreground object has a strong contextual relationship with the scene of the RSI, a scene classification branch is added to the baseline OOD model, and the scene classification result of input RSI is used to exclude the impossible categories. To focus on the hard instances and enhance the consistency between classification and regression, a task-aligned focal loss (TFL) which combines the classification difficulty with the regression loss is proposed, and TFL assigns lager weights to the hard instances and optimizes the classification and regression branches simultaneously. The ablation study proves the effectiveness of scene classification branch, TFL and their combination. The comparisons with 15 and 14 OOD methods on the DOTA and DIOR-R datasets validate the superiority of our method.
Full article
(This article belongs to the Special Issue Advances in Computer Vision and Machine Learning, 2nd Edition)
►▼
Show Figures
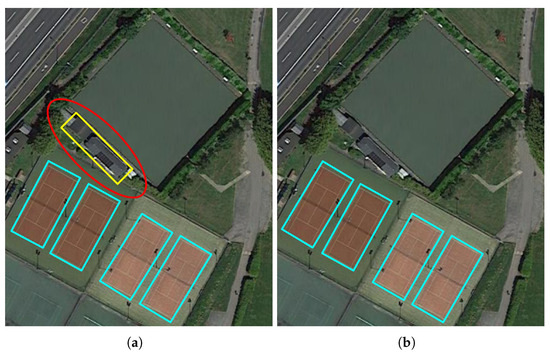
Figure 1
Open AccessArticle
New Results on the Ulam–Hyers–Mittag–Leffler Stability of Caputo Fractional-Order Delay Differential Equations
by
Osman Tunç
Mathematics 2024, 12(9), 1342; https://doi.org/10.3390/math12091342 (registering DOI) - 28 Apr 2024
Abstract
The author considers a nonlinear Caputo fractional-order delay differential equation (CFrDDE) with multiple variable delays. First, we study the existence and uniqueness of the solutions of the CFrDDE with multiple variable delays. Second, we obtain two new results on the Ulam–Hyers–Mittag–Leffler (UHML) stability
[...] Read more.
The author considers a nonlinear Caputo fractional-order delay differential equation (CFrDDE) with multiple variable delays. First, we study the existence and uniqueness of the solutions of the CFrDDE with multiple variable delays. Second, we obtain two new results on the Ulam–Hyers–Mittag–Leffler (UHML) stability of the same equation in a closed interval using the Picard operator, Chebyshev norm, Bielecki norm and the Banach contraction principle. Finally, we present three examples to show the applications of our results. Although there is an extensive literature on the Lyapunov, Ulam and Mittag–Leffler stability of fractional differential equations (FrDEs) with and without delays, to the best of our knowledge, there are very few works on the UHML stability of FrDEs containing a delay. Thereby, considering a CFrDDE containing multiple variable delays and obtaining new results on the existence and uniqueness of the solutions and UHML stability of this kind of CFrDDE are the important aims of this work.
Full article
(This article belongs to the Special Issue Qualitative Analysis of Differential Equations: Theory and Applications)
Open AccessArticle
Shortage Policies for a Jump Process with Positive and Negative Batch Arrivals in a Random Environment
by
Yonit Barron
Mathematics 2024, 12(9), 1341; https://doi.org/10.3390/math12091341 (registering DOI) - 28 Apr 2024
Abstract
We study a continuous-review stock management of a retailer for a single item in a limited storage (buffer) in a random environment. The stock level fluctuates according to two independent compound Poisson processes with discrete amounts of items (batches) that enter and leave
[...] Read more.
We study a continuous-review stock management of a retailer for a single item in a limited storage (buffer) in a random environment. The stock level fluctuates according to two independent compound Poisson processes with discrete amounts of items (batches) that enter and leave the storage facility. The storage facility is controlled by a three-parameter base-stock replenishment policy. All items exceeding the storage capacity are transferred to an unlimited foreign facility. In addition, a restricted backlogging possibility is permitted; additional demands for items are lost sales. We further assume a random shelf life, the possibility of total inventory collapse, and a random lead time. Applying Markov theory, we derive the optimal control parameters minimizing the long-run expected total cost. A sensitivity analysis is conducted focusing on the comparison between the pure lost-sales policy and a partial backordering policy. Accordingly, we identify cases where one policy is cost effective compared to the other, particularly with respect to the batch patterns (sign, rate, average, and variability), and the associated costs.
Full article
(This article belongs to the Special Issue Theoretical and Applied Mathematics in Supply Chain Management)
Open AccessArticle
Two-Stage Probe-Based Search Optimization Algorithm for the Traveling Salesman Problems
by
Md. Azizur Rahman and Jinwen Ma
Mathematics 2024, 12(9), 1340; https://doi.org/10.3390/math12091340 (registering DOI) - 28 Apr 2024
Abstract
As a classical combinatorial optimization problem, the traveling salesman problem (TSP) has been extensively investigated in the fields of Artificial Intelligence and Operations Research. Due to being NP-complete, it is still rather challenging to solve both effectively and efficiently. Because of its high
[...] Read more.
As a classical combinatorial optimization problem, the traveling salesman problem (TSP) has been extensively investigated in the fields of Artificial Intelligence and Operations Research. Due to being NP-complete, it is still rather challenging to solve both effectively and efficiently. Because of its high theoretical significance and wide practical applications, great effort has been undertaken to solve it from the point of view of intelligent search. In this paper, we propose a two-stage probe-based search optimization algorithm for solving both symmetric and asymmetric TSPs through the stages of route development and a self-escape mechanism. Specifically, in the first stage, a reasonable proportion threshold filter of potential basis probes or partial routes is set up at each step during the complete route development process. In this way, the poor basis probes with longer routes are filtered out automatically. Moreover, four local augmentation operators are further employed to improve these potential basis probes at each step. In the second stage, a self-escape mechanism or operation is further implemented on the obtained complete routes to prevent the probe-based search from being trapped in a locally optimal solution. The experimental results on a collection of benchmark TSP datasets demonstrate that our proposed algorithm is more effective than other state-of-the-art optimization algorithms. In fact, it achieves the best-known TSP benchmark solutions in many datasets, while, in certain cases, it even generates solutions that are better than the best-known TSP benchmark solutions.
Full article
(This article belongs to the Section Mathematics and Computer Science)
Open AccessArticle
A New Robust Iterative Scheme Applied in Solving a Fractional Diffusion Model for Oxygen Delivery via a Capillary of Tissues
by
Godwin Amechi Okeke, Akanimo Victor Udo, Nadiyah Hussain Alharthi and Rubayyi T. Alqahtani
Mathematics 2024, 12(9), 1339; https://doi.org/10.3390/math12091339 (registering DOI) - 28 Apr 2024
Abstract
In this paper, we constructed a new and robust fixed point iterative scheme called the UO iterative scheme for the approximation of a contraction mapping. The scheme converges strongly to the fixed point of a contraction mapping. A rate of convergence result is
[...] Read more.
In this paper, we constructed a new and robust fixed point iterative scheme called the UO iterative scheme for the approximation of a contraction mapping. The scheme converges strongly to the fixed point of a contraction mapping. A rate of convergence result is shown with an example, and our scheme, when compared, converges faster than some existing iterative schemes in the literature. Furthermore, the stability and data dependence results are shown. Our new scheme is applied in the approximation of the solution to the oxygen diffusion model. Finally, our results are applied in the approximation of the solution to the boundary value problems using Green’s functions with an example.
Full article
(This article belongs to the Special Issue Variational Inequality and Mathematical Analysis)
Open AccessArticle
On the Integrability of Persistent Quadratic Three-Dimensional Systems
by
Brigita Ferčec, Maja Žulj and Matej Mencinger
Mathematics 2024, 12(9), 1338; https://doi.org/10.3390/math12091338 (registering DOI) - 28 Apr 2024
Abstract
We consider a nine-parameter familiy of 3D quadratic systems,
[...] Read more.
We consider a nine-parameter familiy of 3D quadratic systems,
Open AccessArticle
Depth-Optimized Quantum Circuits for ASCON: AEAD and HASH
by
Yujin Oh, Kyungbae Jang, Anubhab Baksi and Hwajeong Seo
Mathematics 2024, 12(9), 1337; https://doi.org/10.3390/math12091337 (registering DOI) - 27 Apr 2024
Abstract
Quantum computing advancements pose security challenges for cryptography. Specifically, Grover’s search algorithm affects the reduction in the search complexity of symmetric-key encryption and hash functions. Recent efforts have been made to estimate the complexity of Grover’s search and evaluate post-quantum security. In this
[...] Read more.
Quantum computing advancements pose security challenges for cryptography. Specifically, Grover’s search algorithm affects the reduction in the search complexity of symmetric-key encryption and hash functions. Recent efforts have been made to estimate the complexity of Grover’s search and evaluate post-quantum security. In this paper, we propose a depth-optimized quantum circuit implementation for ASCON, including both symmetric-key encryption and hashing algorithms, as a part of the lightweight cryptography standardization by NIST (National Institute of Standards and Technology). As far as we know, this is the first implementation of a quantum circuit for the ASCON AEAD (Authenticated Encryption with Associated Data) scheme, which is a symmetric-key algorithm. Also, our quantum circuit implementation of the ASCON-HASH achieves a reduction of more than 88.9% in the Toffoli depth and more than 80.5% in the full depth compared to the previous work. As per our understanding, the most effective strategy against Grover’s search involves minimizing the depth of the quantum circuit for the target cipher. We showcase the optimal Grover’s search cost for ASCON and introduce a proposed quantum circuit optimized for depth. Furthermore, we utilize the estimated cost to evaluate post-quantum security strength of ASCON, employing the relevant evaluation criteria and the latest advancements in research.
Full article
(This article belongs to the Special Issue Quantum Cryptography and Applications)
Open AccessArticle
Ensemble Approach Using k-Partitioned Isolation Forests for the Detection of Stock Market Manipulation
by
Hugo Núñez Delafuente , César A. Astudillo and David Díaz
Mathematics 2024, 12(9), 1336; https://doi.org/10.3390/math12091336 (registering DOI) - 27 Apr 2024
Abstract
Stock market manipulation, defined as any attempt to artificially influence stock prices, poses significant challenges by causing financial losses and eroding investor trust. The prevalent reliance on supervised learning models for detecting such manipulations, while showing promise, faces notable hurdles due to the
[...] Read more.
Stock market manipulation, defined as any attempt to artificially influence stock prices, poses significant challenges by causing financial losses and eroding investor trust. The prevalent reliance on supervised learning models for detecting such manipulations, while showing promise, faces notable hurdles due to the dearth of labeled data and the inability to recognize novel manipulation tactics beyond those explicitly labeled. This study ventures into addressing these gaps by proposing a novel detection framework aimed at identifying suspicious hourly manipulation blocks through an unsupervised learning approach, thereby circumventing the limitations of data labeling and enhancing the adaptability to emerging manipulation strategies.Our methodology involves the innovative creation of features reflecting the behavior of stocks across various time windows followed by the segmentation of the dataset into k subsets. This setup facilitates the identification of potential manipulation instances via a voting ensemble composed of k isolation forest models, which have been chosen for their efficiency in pinpointing anomalies and their linear computational complexity—attributes that are critical for analyzing vast datasets.Evaluated against eight real stocks known to have undergone manipulation, our approach demonstrated a remarkable capability to identify up to 89% of manipulated blocks, thus significantly outperforming previous methods that do not utilize a voting ensemble. This finding not only surpasses the detection rates reported in prior studies but also underscores the enhanced robustness and adaptability of our unsupervised model in uncovering varied manipulation schemes. Through this research, we contribute to the field by offering a scalable and efficient unsupervised learning strategy for stock manipulation detection, thereby marking a substantial advancement over traditional supervised methods and paving the way for more resilient financial markets.
Full article
(This article belongs to the Special Issue Machine Learning and Finance)
Open AccessFeature PaperArticle
Existence of Solutions to a System of Fractional q-Difference Boundary Value Problems
by
Alexandru Tudorache and Rodica Luca
Mathematics 2024, 12(9), 1335; https://doi.org/10.3390/math12091335 (registering DOI) - 27 Apr 2024
Abstract
We are investigating the existence of solutions to a system of two fractional
We are investigating the existence of solutions to a system of two fractional
(This article belongs to the Special Issue Advances in Differential and Difference Equations and Their Applications)
Open AccessArticle
Green Measures for a Class of Non-Markov Processes
by
Herry P. Suryawan and José L. da Silva
Mathematics 2024, 12(9), 1334; https://doi.org/10.3390/math12091334 (registering DOI) - 27 Apr 2024
Abstract
In this paper, we investigate the Green measure for a class of non-Gaussian processes in
In this paper, we investigate the Green measure for a class of non-Gaussian processes in
(This article belongs to the Special Issue New Advances in Applied Probability and Stochastic Processes)
Open AccessArticle
µ-Integrable Functions and Weak Convergence of Probability Measures in Complete Paranormed Spaces
by
Renying Zeng
Mathematics 2024, 12(9), 1333; https://doi.org/10.3390/math12091333 (registering DOI) - 27 Apr 2024
Abstract
This paper works with functions defined in metric spaces and takes values in complete paranormed vector spaces or in Banach spaces, and proves some necessary and sufficient conditions for weak convergence of probability measures. Our main result is as follows: Let X be
[...] Read more.
This paper works with functions defined in metric spaces and takes values in complete paranormed vector spaces or in Banach spaces, and proves some necessary and sufficient conditions for weak convergence of probability measures. Our main result is as follows: Let X be a complete paranormed vector space and
(This article belongs to the Special Issue Functional Analysis and Mathematical Optimization)
Open AccessArticle
Embedding Secret Data in a Vector Quantization Codebook Using a Novel Thresholding Scheme
by
Yijie Lin, Jui-Chuan Liu, Ching-Chun Chang and Chin-Chen Chang
Mathematics 2024, 12(9), 1332; https://doi.org/10.3390/math12091332 (registering DOI) - 27 Apr 2024
Abstract
In recent decades, information security has become increasingly valued, including many aspects of privacy protection, copyright protection, and digital forensics. Therefore, many data hiding schemes have been proposed and applied to various carriers such as text, images, audio, and videos. Vector Quantization (VQ)
[...] Read more.
In recent decades, information security has become increasingly valued, including many aspects of privacy protection, copyright protection, and digital forensics. Therefore, many data hiding schemes have been proposed and applied to various carriers such as text, images, audio, and videos. Vector Quantization (VQ) compression is a well-known method for compressing images. In previous research, most methods related to VQ compressed images have focused on hiding information in index tables, while only a few of the latest studies have explored embedding data in codebooks. We propose a data hiding scheme for VQ codebooks. With our approach, a sender XORs most of the pixel values in a codebook and then applies a threshold to control data embedding. The auxiliary information generated during this process is embedded alongside secret data in the index reordering phase. Upon receiving the stego codebook and the reordered index table, the recipient can extract the data and reconstruct the VQ-compressed image using the reverse process. Experimental results demonstrate that our scheme significantly improves embedding capacity compared to the most recent codebook-based methods. Specifically, we observe an improvement rate of 223.66% in a small codebook of size 64 and an improvement rate of 85.19% in a codebook of size 1024.
Full article
(This article belongs to the Special Issue Advances in Mathematical Cryptography and Information Security toward Industry 5.0)
Open AccessArticle
Enhanced YOLOX with United Attention Head for Road Detetion When Driving
by
Yuhuan Wu and Yonghong Wu
Mathematics 2024, 12(9), 1331; https://doi.org/10.3390/math12091331 (registering DOI) - 27 Apr 2024
Abstract
►▼
Show Figures
Object detection plays a crucial role in autonomous driving assistance systems. It requires high accuracy for prediction, a small size for deployment on mobile devices, and real-time inference speed to ensure safety. In this paper, we present a compact and efficient algorithm called
[...] Read more.
Object detection plays a crucial role in autonomous driving assistance systems. It requires high accuracy for prediction, a small size for deployment on mobile devices, and real-time inference speed to ensure safety. In this paper, we present a compact and efficient algorithm called YOLOX with United Attention Head (UAH-YOLOX) for detection in autonomous driving scenarios. By replacing the backbone network with GhostNet for feature extraction, the model reduces the number of parameters and computational complexity. By adding a united attention head before the YOLO head, the model effectively detects the scale, position, and contour features of targets. In particular, an attention module called Spatial Self-Attention is designed to extract spatial location information, demonstrating great potential in detection. In our network, the IOU Loss (Intersection of Union) has been replaced with CIOU Loss (Complete Intersection of Union). Further experiments demonstrate the effectiveness of our proposed methods on the BDD100k dataset and the Caltech Pedestrian dataset. UAH-YOLOX achieves state-of-the-art results by improving the detection accuracy of the BDD100k dataset by 1.70% and increasing processing speed by 3.37 frames per second (FPS). Visualization provides specific examples in various scenarios.
Full article
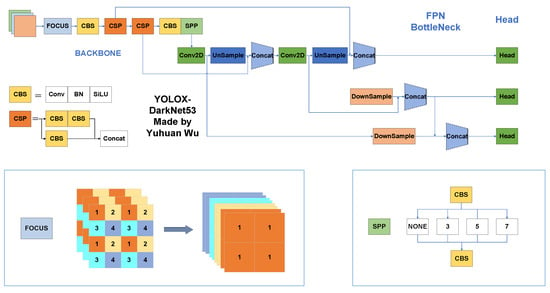
Figure 1
Open AccessArticle
Deep-Representation-Learning-Based Classification Strategy for Anticancer Peptides
by
Shujaat Khan
Mathematics 2024, 12(9), 1330; https://doi.org/10.3390/math12091330 (registering DOI) - 27 Apr 2024
Abstract
Cancer, with its complexity and numerous origins, continues to provide a huge challenge in medical research. Anticancer peptides are a potential treatment option, but identifying and synthesizing them on a large scale requires accurate prediction algorithms. This study presents an intuitive classification strategy,
[...] Read more.
Cancer, with its complexity and numerous origins, continues to provide a huge challenge in medical research. Anticancer peptides are a potential treatment option, but identifying and synthesizing them on a large scale requires accurate prediction algorithms. This study presents an intuitive classification strategy, named ACP-LSE, based on representation learning, specifically, a deep latent-space encoding scheme. ACP-LSE can demonstrate notable advancements in classification outcomes, particularly in scenarios with limited sample sizes and abundant features. ACP-LSE differs from typical black-box approaches by focusing on representation learning. Utilizing an auto-encoder-inspired network, it embeds high-dimensional features, such as the composition of g-spaced amino acid pairs, into a compressed latent space. In contrast to conventional auto-encoders, ACP-LSE ensures that the learned feature set is both small and effective for classification, giving a transparent alternative. The suggested approach is tested on benchmark datasets and demonstrates higher performance compared to the current methods. The results indicate improved Matthew’s correlation coefficient and balanced accuracy, offering insights into crucial aspects for developing new ACPs. The implementation of the proposed ACP-LSE approach is accessible online, providing a valuable and reproducible resource for researchers in the field.
Full article
(This article belongs to the Special Issue Artificial Intelligence for Biomedical Applications)
►▼
Show Figures
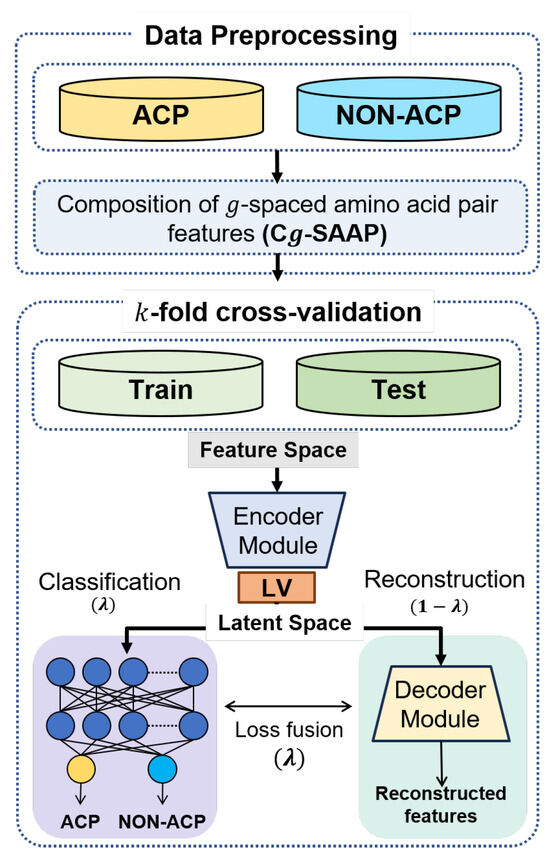
Figure 1
Open AccessFeature PaperArticle
Unraveling the Complexity of Inverting the Sturm–Liouville Boundary Value Problem to Its Canonical Form
by
Natanael Karjanto and Peter Sadhani
Mathematics 2024, 12(9), 1329; https://doi.org/10.3390/math12091329 (registering DOI) - 26 Apr 2024
Abstract
The Sturm–Liouville boundary value problem (SLBVP) stands as a fundamental cornerstone in the realm of mathematical analysis and physical modeling. Also known as the Sturm–Liouville problem (SLP), this paper explores the intricacies of this classical problem, particularly the relationship between its canonical and
[...] Read more.
The Sturm–Liouville boundary value problem (SLBVP) stands as a fundamental cornerstone in the realm of mathematical analysis and physical modeling. Also known as the Sturm–Liouville problem (SLP), this paper explores the intricacies of this classical problem, particularly the relationship between its canonical and Liouville normal (Schrödinger) forms. While the conversion from the canonical to Schrödinger form using Liouville’s transformation is well known in the literature, the inverse transformation seems to be neglected. Our study attempts to fill this gap by investigating the inverse of Liouville’s transformation, that is, given any SLP in the Schrödinger form with some invariant function, we seek the SLP in its canonical form. By closely examining the second Paine–de Hoog–Anderson (PdHA) problem, we argue that retrieving the SLP in its canonical form can be notoriously difficult and can even be impossible to achieve in its exact form. Finding the inverse relationship between the two independent variables seems to be the main obstacle. We confirm this claim by considering four different scenarios, depending on the potential and density functions that appear in the corresponding invariant function. In the second PdHA problem, this invariant function takes a reciprocal quadratic binomial form. In some cases, the inverse Liouville transformation produces an exact expression for the SLP in its canonical form. In other situations, however, while an exact canonical form is not possible to obtain, we successfully derived the SLP in its canonical form asymptotically.
Full article
(This article belongs to the Special Issue Differential Equations with Boundary Value Problems: Theory and Applications)
Open AccessArticle
Efficient List Intersection Algorithm for Short Documents by Document Reordering
by
Lianyin Jia, Dongyang Li, Haihe Zhou and Fengling Xia
Mathematics 2024, 12(9), 1328; https://doi.org/10.3390/math12091328 (registering DOI) - 26 Apr 2024
Abstract
List intersection plays a pivotal role in various domains such as search engines, database systems, and social networks. Efficient indexes and query strategies can significantly enhance the efficiency of list intersection. Existing inverted index-based algorithms fail to utilize the length information of documents
[...] Read more.
List intersection plays a pivotal role in various domains such as search engines, database systems, and social networks. Efficient indexes and query strategies can significantly enhance the efficiency of list intersection. Existing inverted index-based algorithms fail to utilize the length information of documents and require excessive list intersections, resulting in lower efficiency. To address this issue, in this paper, we propose the LDRpV (Length-based Document Reordering plus Verification) algorithm. LDRpV filters out documents that are unlikely to satisfy the intersection results by reordering documents based on their length, thereby reducing the number of candidates. Additionally, to minimize the number of list intersection operations, an intersection and verification strategy is designed, where only the first
(This article belongs to the Special Issue Advances of Computer Algorithms and Data Structures)
Open AccessArticle
Fast Eigenvalue Decomposition of Arrowhead and Diagonal-Plus-Rank-k Matrices of Quaternions
by
Thaniporn Chaysri, Nevena Jakovčević Stor and Ivan Slapničar
Mathematics 2024, 12(9), 1327; https://doi.org/10.3390/math12091327 - 26 Apr 2024
Abstract
Quaternions are a non-commutative associative number system that extends complex numbers, first described by Hamilton in 1843. We present algorithms for solving the eigenvalue problem for arrowhead and DPRk (diagonal-plus-rank-k) matrices of quaternions. The algorithms use the Rayleigh Quotient Iteration with
[...] Read more.
Quaternions are a non-commutative associative number system that extends complex numbers, first described by Hamilton in 1843. We present algorithms for solving the eigenvalue problem for arrowhead and DPRk (diagonal-plus-rank-k) matrices of quaternions. The algorithms use the Rayleigh Quotient Iteration with double shifts (RQIds), Wielandt’s deflation technique and the fact that each eigenvector can be computed in
(This article belongs to the Section Computational and Applied Mathematics)
Open AccessFeature PaperArticle
A Three-Dimensional Velocity Field Related to a Generalized Third-Grade Fluid Model
by
Fernando Carapau, Paulo Correia and Gracino Rodrigues
Mathematics 2024, 12(9), 1326; https://doi.org/10.3390/math12091326 - 26 Apr 2024
Abstract
In this work, we propose a new three-dimensional constitutive equation related to a third-grade fluid. This proposal is based on experimental work for which the viscosity term and the terms related to viscoelasticity may depend on the shear rate, in accordance with a
[...] Read more.
In this work, we propose a new three-dimensional constitutive equation related to a third-grade fluid. This proposal is based on experimental work for which the viscosity term and the terms related to viscoelasticity may depend on the shear rate, in accordance with a power-law type model. The numerical implementation of this fluid model is rather demanding in terms of computational calculation and, in this sense, we use the Cosserat theory related to fluid dynamics, which makes the transition from the three-dimensional fluid model to a one-dimensional fluid model for a specific geometry under study which, in this case, is a straight tube with constant circular cross-section. Based on this approximation theory, the one-dimensional fluid model is solved by assuming an ordinary differential equation involving: an unsteady mean pressure gradient; an unsteady volume flow rate; the Womersley number; and the viscosity and viscoelasticity parameters. Consequently, for specific data, and using the Runge–Kutta method, we can obtain the solution for the unsteady volume flow rate and we can present simulations to the three-dimensional velocity field.
Full article
(This article belongs to the Section Mathematical Physics)
Open AccessArticle
Initial Coefficient Bounds Analysis for Novel Subclasses of Bi-Univalent Functions Linked with Lucas-Balancing Polynomials
by
Sondekola Rudra Swamy, Daniel Breaz, Kala Venugopal, Mamatha Paduvalapattana Kempegowda, Luminita-Ioana Cotîrlă and Eleonora Rapeanu
Mathematics 2024, 12(9), 1325; https://doi.org/10.3390/math12091325 - 26 Apr 2024
Abstract
We investigate some subclasses of regular and bi-univalent functions in the open unit disk that are associated with Lucas-Balancing polynomials in this work. For functions that belong to these subclasses, we obtain upper bounds on their initial coefficients. The Fekete–Szegö problem is also
[...] Read more.
We investigate some subclasses of regular and bi-univalent functions in the open unit disk that are associated with Lucas-Balancing polynomials in this work. For functions that belong to these subclasses, we obtain upper bounds on their initial coefficients. The Fekete–Szegö problem is also discussed. Along with presenting some new results, we also explore pertinent connections to earlier findings.
Full article

Journal Menu
► ▼ Journal Menu-
- Mathematics Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Instructions for Authors
- Special Issues
- Topics
- Sections & Collections
- Article Processing Charge
- Indexing & Archiving
- Editor’s Choice Articles
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Society Collaborations
- Conferences
- Editorial Office
Journal Browser
► ▼ Journal BrowserHighly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Axioms, Computation, MCA, Mathematics, Symmetry
Mathematical Modeling
Topic Editors: Babak Shiri, Zahra AlijaniDeadline: 31 May 2024
Topic in
Algorithms, Axioms, Fractal Fract, Mathematics, Symmetry
Fractal and Design of Multipoint Iterative Methods for Nonlinear Problems
Topic Editors: Xiaofeng Wang, Fazlollah SoleymaniDeadline: 30 June 2024
Topic in
Algorithms, Computation, Information, Mathematics
Complex Networks and Social Networks
Topic Editors: Jie Meng, Xiaowei Huang, Minghui Qian, Zhixuan XuDeadline: 31 July 2024
Topic in
Algorithms, Future Internet, Information, Mathematics, Symmetry
Research on Data Mining of Electronic Health Records Using Deep Learning Methods
Topic Editors: Dawei Yang, Yu Zhu, Hongyi XinDeadline: 31 August 2024

Conferences
Special Issues
Special Issue in
Mathematics
Advances in the Mathematics of Ecological Modelling
Guest Editors: Dmitrii O. Logofet, Larisa Khanina, Pavel GrabarnikDeadline: 30 April 2024
Special Issue in
Mathematics
Advances in Linear Recurrence System
Guest Editors: Lorentz Jäntschi, Virginia NiculescuDeadline: 15 May 2024
Special Issue in
Mathematics
New Trends on Boundary Value Problems
Guest Editors: Miklós Rontó, András Rontó, Nino Partsvania, Bedřich Půža, Hriczó KrisztiánDeadline: 31 May 2024
Special Issue in
Mathematics
Applications of Fuzzy Modeling in Risk Management
Guest Editors: Edit Toth-Laufer, László PokorádiDeadline: 20 June 2024
Topical Collections
Topical Collection in
Mathematics
Topology and Foundations
Collection Editors: Lorentz Jäntschi, Dušanka Janežič
Topical Collection in
Mathematics
Multiscale Computation and Machine Learning
Collection Editors: Yalchin Efendiev, Eric Chung
Topical Collection in
Mathematics
Theoretical and Mathematical Ecology
Collection Editor: Yuri V. Tyutyunov